
Examining the Meraki Fullstack (Part 1)
Meraki was founded in 2006 by two MIT graduates with funding from Google and Sequoia Capital. The focus in Meraki's formative years was building a wireless solution that combined cloud-based ease of use and administration with analytics and reporting. In this article we will focus on the Cisco Meraki Wireless solution's approach to achieving high performance, security, and location analytics.
From the start, the Meraki Dashboard set the brand apart. The dashboard gave administrators a centralized portal to view and manage their wireless from anywhere they could access Internet. As the product advanced and became a market leader, the big players took notice, and in 2012 Cisco purchased Meraki. Since the acquisition, Cisco has allowed Meraki to prosper as an independent brand enhanced by Cisco's routing and security knowledge and expertise. The brand has expanded dramatically, bringing their vision of simplicity, analytics, and performance to newer product lines. The Meraki platform now includes data switches, firewalls, mobile device management, and security cameras on one consolidated cloud management platform. Despite the expanded portfolio and value of a consolidated solution, each of the products works as a stand-alone that neatly folds into an existing data strategy.
Meraki WiFi - High Performance Wireless
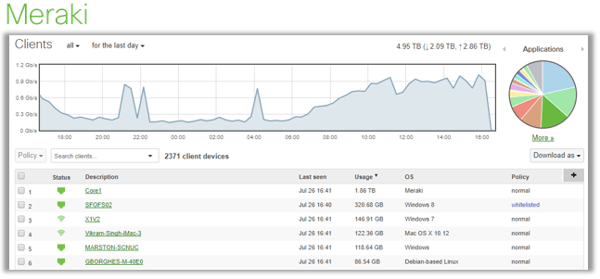
Meraki is well known for their ease of management, deployment, and advanced analytics. Meraki's hardware has seen dramatic expansion and improvement in the last 5 years. They offer a range of devices that support environments ranging from outdoor deployments to stadium type environments that have a high concentration of users per access point. Addressing interference on a Wireless LAN has been increasing in complexity as more and more radios hit the airwaves. Meraki uses a dedicated 3rd radio in their access points to identify and measure both rogue APs and non-WiFi interference, then uses the data to coordinate channel management to avoid colliding packets. Each access point has its own Deep Packet Inspection engine that can identify applications via Layer 7 fingerprinting. This information can then be used to control QoS at the edge. This feature allows administrators to easily prioritize critical applications like voice, video, or POS systems, while blocking or capping speeds to non-critical applications like Netflix or Pandora.
While Matrix Networks does not typically advise clients to rely on meshing networks to support their devices, there are scenarios where it makes sense to utilize Meraki's flavor of meshing technology. Meraki’s Mesh is unique because it is constantly measuring the health of each link and will steer traffic accordingly. Using directional antennas and smart design, meshing can be used to cover areas where cable runs are not possible. The meshing on Meraki is constantly maintained whether used as a primary route or, more commonly, as a failover in the event a switch port fails or cabling is damaged. Meraki also plays well with the prickly Bonjour protocol from Apple. The platform supports Bonjour devices and traffic natively, selectively bridging traffic to AirPlay, AirPrint, and Apple Filing Protocol (RIP) on your subnet of choice.
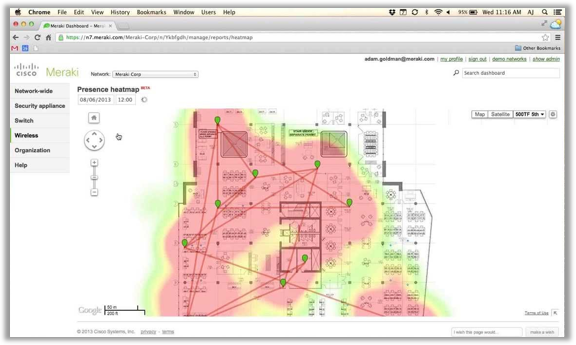
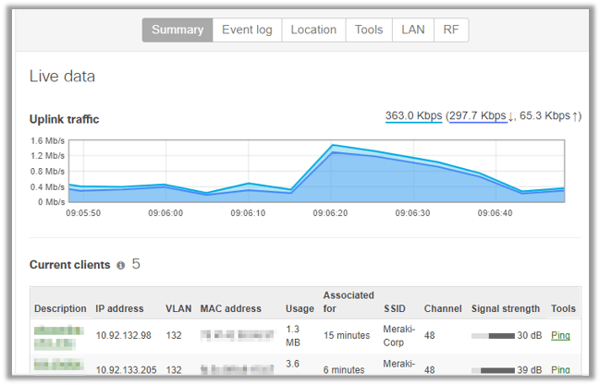
Measuring the performance of the wireless network and providing simple remediation is a strong suit of Meraki’s. The event logs and connectivity graphs are a good starting point, giving you visibility into the usage, associations, dissociations, de-authentications, timestamps for building of timeline, RSSI values (including historical signal strength), and any AP or SSID events that occurred. Heatmaps are included in the portal, giving you real-time visibility into the performance of the network without a professional rolling a truck to site. Remote troubleshooting and information gathering is a cinch, with the ability for administrators to perform remote packet captures, reboot specific devices, run physical cable tests and ping tests. The Meraki Wireless Health product, soon to be released, takes this one step further by providing the results of your wireless health in an easily digestible dashboard. Using this tool will quickly help you answer the following questions: Can users access the wireless networks successfully? Are connected guests having a good experience? Are any access points overloaded or in need of optimization? By answering these questions before they become user issues, administrators stay ahead of the curve.
Meraki WiFi | Focus on Security
Security is commonly overlooked when choosing and deploying WiFi networks, exposing your organization to a variety of threats. Most administrators will roll-out PSK or the more advanced EAP/PEAP authentication methods and then walk away. This is really the tip of the WiFi security iceberg. A serious professional will secure their WiFi with WIPS (Wireless Intrusion Prevention System) that can detect Route SSIDs and Rouge APs and then contain them. Rogue SSIDs and Access Points are a concern in two ways, the first is an employee that plugs in an access point not supported by the IT department. A Rouge Access Point is when someone plugs in a random Access Point into the corporate LAN. This creates a network security issue by allowing traffic to bypass security and authentication and essentially allow anyone to connect directly to the wired network. The second challenge related to Rogue APs is more of a malicious nature. A Rogue Access Point can be configured to spoof an existing SSID, drawing in users who believe they are connecting to an approved network. Once a user has joined the Rogue SSID, a variety of concerns come into play, including man-in-the-middle attacks to steal credentials, and it might even provide a conduit for theft of sensitive company information. Meraki combats this issue without manual intervention by first identifying the bad actor, then sending a flood of de-authentication packets to prevent the clients from connecting.
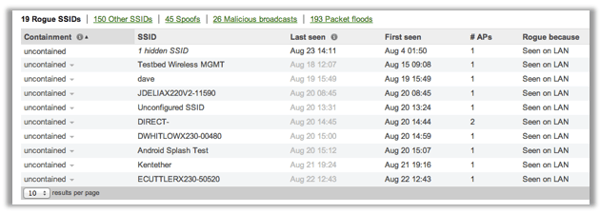
Once you have closed loopholes for data breaches, a security minded individual needs to think about activities that could render the network useless with malicious broadcasts or packet floods in a denial of service attack. The Meraki solution identifies these events, alerts, and then provides reporting for remediation. This capability allows administrators to identify the issue quickly and remove the offender from the network, minimizing the impact to end-users. With all access points having a DPI engine, they can also natively filter for adult content, giving your team the freedom to roll-out a guest network outside the firewall and still prevent inappropriate network usage.
Location, Location, Location...
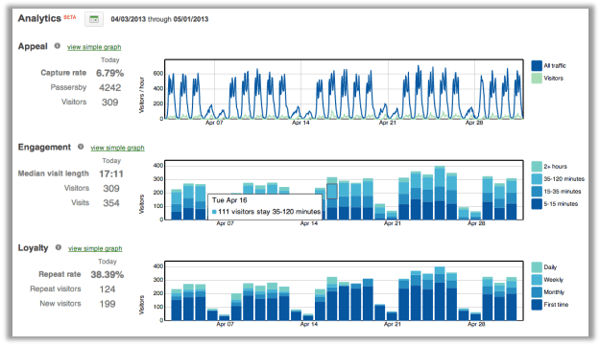
An underappreciated feature of WiFi is the capability to track and monitor devices, track the movement of customers or staff, and provide analytics. Meraki’s access points are constantly gathering location data including the MAC address of clients as they associate, probing MAC client time stamps, and RSSI info. Using this information Meraki reports on the following
-
Capture Rate – This measures the percentage of your foot traffic that is passerby vs visitor traffic. This can be used to identify poor performing segments of a retail store or the number of people who pass a coffee shop without entering, for example.
-
Median Visit Length – This metric provides managers vision into the amount of time spent in your store, office, bar, or any other space. For service centers, the measurement might be used to see how quickly clients receive service; for a bar it could be a measure of how long customers stay vs what they spend.
-
Repeat Visit Rate – This metric looks for devices that repeatedly surface on the wireless network, giving visibility into customer loyalty and buying behaviors. Understanding when repeat customers visit, how often, and for how long gives your marketing and retail teams a new tool for success.
-
Total Visits for a Site – Accounting for the total visitors into a store, hotel, or retail shop is powerful. Using this data combined with sales data gives you more a more accurate understanding of spend per person and the effectiveness of your offerings.
The data collected in Meraki can also integrate to 3rd party applications like customer relationship management platforms. With the API integration, customers on loyalty programs with a native app can receive push notifications of special offers or discounts based on their physical location. For example, when a hotel guest leaves their room and passes the Spa, a notification is pushed to their phone offering 25% off massage and pedicure packages booked before 2:00. This type of integration allows businesses to align more closely with their clients by making the correct offer at the perfect time.
Bluetooth is another tool in Meraki’s solution for location type services. Bluetooth beacons, which require very little power, can be placed on devices like AEDs, media carts, or expensive merchandise to track their movement and current location. Using the Bluetooth beacons and embedded applications on smart devices retailers can push notifications about loyalty programs and special discounts for clients or notification of a VIP guest's location, guest departure from a hotel room, or general data (name, buying habits etc.) about clients as they enter a retail store, allowing staff to greet them by name.
Meraki Wireless has done an excellent job of layering powerful applications and tools on top of their easy to manage WiFi platform. Although almost every wireless provider can provide these features via add-on products – native or 3rd party – the Meraki platform is the only one to embed all of these tools in one cloud-based portal natively.
Why Matrix Networks Partners with Meraki?
Although Meraki products come at a premium, we have discovered the value of the analytics, performance, troubleshooting tools, and ease of use. All of which make Meraki an excellent value, especially when paired with the full-stack for complete network control. To learn more about Meraki’s platform you can schedule a demo with our team, watch a webinar (and receive a free AP), and even try it yourself on a trial. As a Premier Cisco Partner, Matrix Networks is here to assist in anyway we can. Let us know how we can help.
Examining the Meraki Fullstack (Part 2)
True to Cisco form, the switches all have non-blocking backplanes, meaning that all ports can be used at bidirectional max capacity simultaneously; most of the competitors offer underpowered backplanes to reduce cost.
Author: Kyle Holmes



.svg%20(1).png?width=55&name=1200px-Logo_of_YouTube_(2015-2017).svg%20(1).png)

