Examining the Meraki Fullstack (Part 3)
Meraki was founded in 2006 by two MIT graduates with funding from Google and Sequoia Capital. The focus in Meraki's formative years was building a wireless solution that combined cloud-based ease of use and administration with analytics and reporting. From the start, the Meraki Dashboard set the brand apart. The dashboard gave administrators a centralized portal to view and manage their wireless from anywhere they could access Internet. Incredible right!?!
As the product advanced and became a market leader, the big players took notice, and in 2012 Cisco purchased Meraki. Since the acquisition, Cisco has allowed Meraki to prosper as an independent brand enhanced by Cisco's routing and security knowledge and expertise. The brand has expanded dramatically, bringing their vision of simplicity, analytics, and performance to newer product lines. The Meraki platform now includes data switches, firewalls, mobile device management, and security cameras on one consolidated cloud management platform. Despite the expanded portfolio and value of a consolidated solution, each of the products works as a stand-alone that neatly folds into an existing data strategy. In this article we will focus on the Cisco Meraki Firewall solution's approach to building a secure, highly available network that remains simple to manage.
Take it Easy!
Meraki's MX series is a great combination of Cisco's world class security with the established strategy of simple management and roll-outs. It should be recognized upfront that Meraki's security features are not equal to Cisco's traditional firewall solutions. For the majority of businesses, the Meraki's embedded Unified Threat Management system will be an improvement on existing security, but companies that have more complex needs should get the help of a professional to design the integration of a traditional or cloud-based firewall.
Rolling out a new location with Meraki's MX solution is simple, starting with the ability to program the gear while it is still in transit. After you purchase a Meraki appliance, an order number is sent with tracking information and allows the administrator to log in and claim the equipment and begin programming before any equipment arrives. Once the equipment is connected to the Internet, it reaches out to the cloud controller and downloads it’s configuration. There is no need to remote into each device and establish IPSEC tunnels as this is accomplished through the portal in just a couple of clicks, no matter the number of connections through automagical mesh VPN.
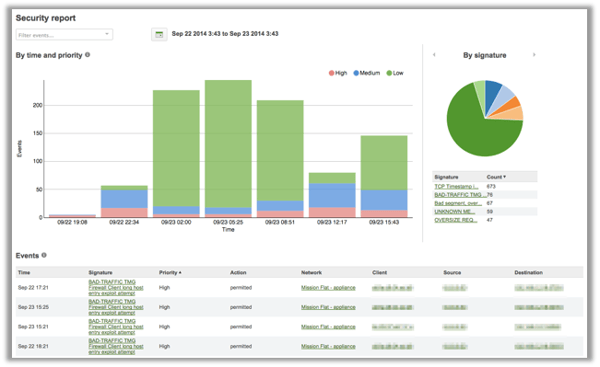
Cisco has had a huge impact on the Meraki product line, everything from physical equipment to routing protocols. In our opinion the biggest advantage the relationship brings is the security platforms Cisco provides and embeds in the MX ecosystem. The security features include things like Anti-malware, Anti-phishing, IPS/IDS (Intrusion prevention and detection), botnet C&C blocking, and more. The IPS/IDS solution uses Cisco's Sourcefire Snort, the same software used on Cisco's traditional ASA firewall solutions. IPS is implemented using rulesets, pre-defined security policies that determine the level of protection needed. The rulesets are updated daily to ensure protection against the latest vulnerabilities including exploits, viruses, rootkits, and more. The anti-malware solution utilizes Cisco’s AMP (Advance Malware Protection), which is arguably the strongest malware protection, and it's included with the Meraki MX appliance's Advanced license. AMP is being constantly updated by the 250+ security specialists in Cisco’s Talos group. These updates are automatically pushed down to the Meraki cloud within an hour without manual staging or patching needed. With Meraki's unique cloud-based design, these firmware updates are applied on average within 12 hours of discovery, a huge improvement on the industry average of more than 100 days.
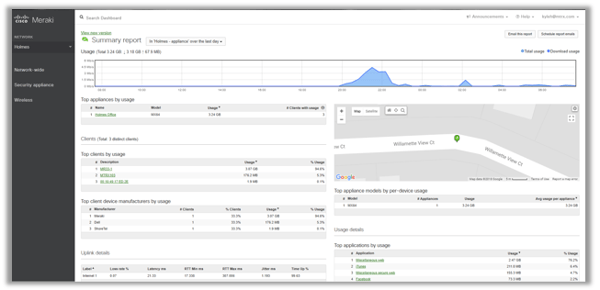
Gathering data about security is incredibly important in the prevention of data leak and breaches. Meraki offers both real-time and historical reports on detected security threats with links to specific remediation by linking to CVE, TechNet, and other resources. Those concerned about securing their network can look at broad reports and then drill into specific networks for detailed reporting on events and threats. These reports can be a fantastic synopsis to provide to management giving visibility into the trends and overall vulnerability over time.
Valued Insight
A significant advantage of the Meraki platform is the availability of analytics that can be used for identifying and remediating network issues. At the root of this data is Layer 7 visibility, giving admins the capability to classify and control traffic based on the specific application, user, device, or network. Once traffic flow is identified, it is simple to block, rate limit, or prioritize your applications, improving the end-user experience. The reports provided are also useful for management in identifying employee internet behaviors. For example, how much of your company bandwidth is being used on Facebook or Netflix? Is it worth blocking these services? Establishing policies is simple, flexible, and easily set for user groups in Active Directory, for types of devices or for specific users on the system. Content filtering in the MX is a drop-down, allowing you to block general categories from pornographic and violent sites to financial services. This feature also allows you to black or whitelist specific sites as you choose.
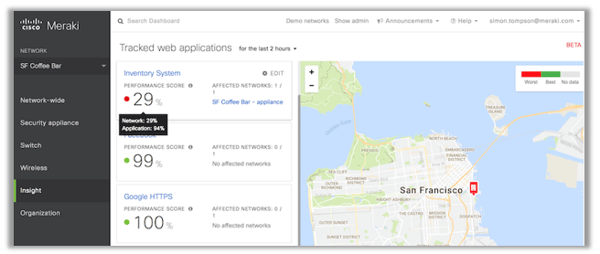
The Insights product from Meraki is an add-on that uses the MX appliances as data collectors. This analytics platform is designed to provide end-to-end visibility of how your users are experiencing network and application performance. Evaluating all the steps, from user to application, by collecting data on both applications web-based or otherwise, Insights provides us a unique snapshot allowing us to answer the question “why is it running sooooo SLOW??” Using primarily per-flow goodput and application response time, the solution will provide a Performance Score and determine what applications or network devices need attention. Once trouble is spotted, the administrator simply drills into the specific application or user and begins reviewing the Insights provided, whether that is WAN loss, latency, application response time, or other trouble, all in mere seconds.
Stacking Up
Meraki’s MX appliance is a powerful tool in and of itself. When combined with the rest of the Meraki Stack, data switches, wireless access points, mobile device management, and security cameras, big value begins to take shape. Managing your network from device connectivity to security is all performed in a single web-based portal with no CLI language to learn. The physical equipment ranges from teleworker and small branch devices to Enterprise class data center equipment. The MX can be virtualized in both Azure and AWS, extending the power of Meraki’s platform to your public cloud to ensure consistent connectivity and security in everything your organization does. With Meraki’s MX appliance, administrators can breathe easy knowing the security of the network is up to date with analytics to back it up.
Why Matrix Networks Partners with Meraki?
Although Meraki products come at a premium, we have discovered the value of the analytics, performance, troubleshooting tools, and ease of use. All of which make Meraki an excellent value, especially when paired with the full-stack for complete network control. To learn more about Meraki’s platform you can schedule a demo with our team, watch a webinar (and receive a free AP), and even try it yourself on a trial. As a Premier Cisco Partner, Matrix Networks is here to assist in anyway we can. Let us know how we can help.
Examining the Meraki Fullstack (Part 4)
A signature feature of the MV lineup is the use of local storage on the camera itself, eliminating the need for a centralized or cloud based “NVR” solution. The Meraki dashboard accesses the streams in an on-demand fashion.
Author: Kyle Holmes


.svg%20(1).png?width=55&name=1200px-Logo_of_YouTube_(2015-2017).svg%20(1).png)

